The National Cybersecurity Center (NCSC) warns of a vulnerability in KeePass password manager. Malicious people can use the vulnerability to gain access to data stored in KeePass.
The problem (NCSC-2023-0044) is in the configuration of KeePass, which stores the password manager unencrypted. Those with malicious intent can modify the configuration, for example, adding a malicious export rule. If the user opens the KeePass database later, that database causes KeePass to export the stored data to the attacker.
The developer does not want to fix the leak
The National Food Security Center (NCSC) warns that a proof-of-concept is available, which would simplify exploitation of the vulnerability. However, the developer of KeePass does not want to fix the leak. The developer’s position is that once a malicious attacker gains access to the victim’s system, there is no reasonable way to prevent the stored data from being stolen.
KeePass offers an option to force certain configurations thus preventing abuse of the vulnerability. This can be done using what is called a forced configuration file. NCSC advises organizations to use these options. More information here Available.

“Thinker. Coffeeaholic. Award-winning gamer. Web trailblazer. Pop culture scholar. Beer guru. Food specialist.”




More Stories
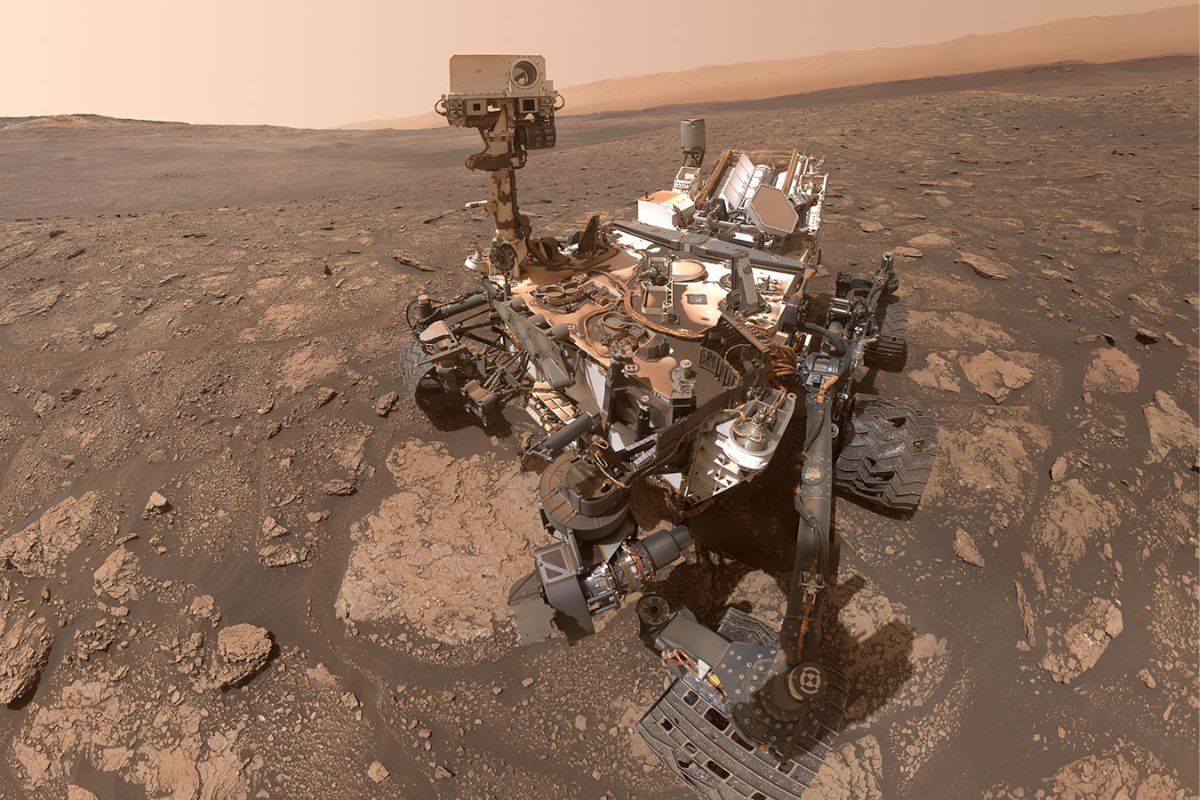
It seems that scientists finally know what happens to methane on Mars
Mozilla warns WhatsApp against misinformation in the elections
6. We are not afraid enough of artificial intelligence